Airtel users can able to use facebook free of cost. Airtel offers this scheme for 9 regional languages in India. Customers can use facebook via application or their defualt mobile web browser. As in this offer you can access all the features of facebook like chatting,commenting ,uploading and more. But the disadvantage is a customer can only use 30 MB in a month and how much days this offer will valid not announced by Airtel. So this is not a happy news!!!
Monday 30 December 2013
Sunday 29 December 2013
How to find serial keys from Google search
Posted By:
I am Nothing
on 21:47
Hello guys , if you need serial number for any kind of software-its not difficult to find from google. Here have an easy method to search the serial key for your need. its just simple follow the below steps.
- Go to google.com
- in the search box write your software name (for which software's serial you need) first and add "94fbr" with the search.
- for eg- if you need the serial key of microsoft office , then write "microsoft office 94fbr" in google search without double quotes and click on search button.
Now you will get many site with the most related answers from google. This is very simple method to find the serial key and most of the result are working. so you no need to find the serial key from a specified website.
How to restore the files from a pendrive/mc without format
Posted By:
I am Nothing
on 20:46
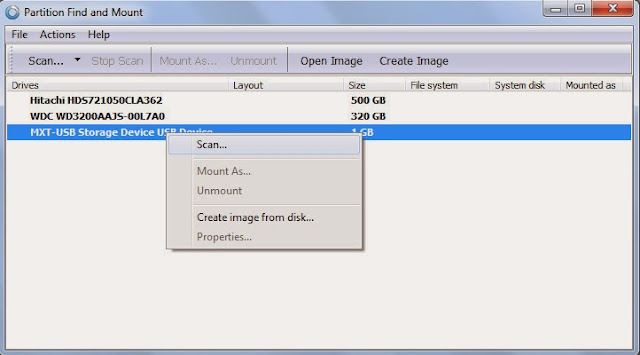
You might face the problem of this. If you put your pendrive or memory card into your pc/laptop the computer says that should format the device to use. But the device may contain your files and its may need you. That case you should recover the files first and format. for that purpose we use a software that call "find and Mount".
About find and mount
Partition Find & Mount implements a new concept of deleted or lost partition recovery. It works in the most convenient way possible — by locating and mountingpartitions into the system, thus making those lost partitions available to you like any generic disk volume. Partition Find & Mount will also work in case any Boot Record (including the Master Boot Record) is missing, damaged or overwritten.
To mount the device follow the steps below
step 1: Download Find and mount - its a free software
step 2: Install it and open.
step 3: now you can see the box like this if there have a secondery media storage.
right click on that select scan.
step 4: select first option and scan.
step 5: now you can see like this box.
step 6: Then you can see the partitioned location like this. righ click on that and select mount as.
step 7: And select drive letter which you want (anything). and ok.
step 7: Now its ready to see in your my computer with the drive letter. Enjoy!!
Saturday 28 December 2013
Against Malware and Virus-Download Bitdefender total security 2014
Posted By:
I am Nothing
on 21:09
Bitdefender Total Security
Bitdefender Total Security is the acknowledged Antivirus of the Year. With a non-intrusive and extremely fast scanning technology, it offers the ultimate silent security against e-threats.
- Ultimate anti-malware defense for your data
- Extremely fast. Non-intrusive. With Bitdefender Photon™
- Guards your online transactions. Protects your digital identity.
- Reveals your kids’ online activities. Restricts them when necessary.
- Safely stores your information online and syncs it between devices
- Safeguards laptops and netbooks in case of loss or theft
( Bitdefender Total security )
Malware attack of a computer
Posted By:
I am Nothing
on 20:56
What is Malware
Malware, short for malicious software, is software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. It can appear in the form of code, scripts, active content, and other software. 'Malware' is a general term used to refer to a variety of forms of hostile or intrusive software.
Malware includes computer viruses, ransomware, worms, trojan horses, rootkits, keyloggers, dialers, spyware, adware, malicious BHOs, rogue security software and other malicious programs; the majority of active malware threats are usually worms or trojans rather than viruses. In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states. Malware is different from defective software, which is a legitimate software but contains harmful bugs that were not corrected before release. However, some malware is disguised as genuine software, and may come from an official company website in the form of a useful or attractive program which has the harmful malware embedded in it along with additional tracking software that gathers marketing statistics.
Software such as anti-virus, anti-malware, and firewalls are relied upon by users at home, small and large organizations around the globe to safeguard against malware attacks which helps in identifying and preventing the further spread of malware in the network.
How They are attack
Malware, short for malicious software, is software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. It can appear in the form of code, scripts, active content, and other software. 'Malware' is a general term used to refer to a variety of forms of hostile or intrusive software.
Malware includes computer viruses, ransomware, worms, trojan horses, rootkits, keyloggers, dialers, spyware, adware, malicious BHOs, rogue security software and other malicious programs; the majority of active malware threats are usually worms or trojans rather than viruses. In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states. Malware is different from defective software, which is a legitimate software but contains harmful bugs that were not corrected before release. However, some malware is disguised as genuine software, and may come from an official company website in the form of a useful or attractive program which has the harmful malware embedded in it along with additional tracking software that gathers marketing statistics.
Software such as anti-virus, anti-malware, and firewalls are relied upon by users at home, small and large organizations around the globe to safeguard against malware attacks which helps in identifying and preventing the further spread of malware in the network.
How They are attack
Trojan horses
For a malicious program to accomplish its goals, it must be able to run without being detected, shut down, or deleted. When a malicious program is disguised as something normal or desirable, users may willfully install it without realizing it. This is the technique of the Trojan horse or trojan. In broad terms, a Trojan horse is any program that invites the user to run it, concealing harmful or malicious code. The code may take effect immediately and can lead to many undesirable effects, such as deleting the user's files or installing additional harmful software.
One of the most common ways that spyware is distributed is as a Trojan horse, bundled with a piece of desirable software that the user downloads from the Internet. When the user installs the software, the spyware is installed along with it. Spyware authors who attempt to act in a legal fashion may include an end-user license agreement that states the behavior of the spyware in loose terms, which users may not read or understand.
DOWNLOAD ANTIVIRUS FREE
Nokia Android phone Introduction
Posted By:
I am Nothing
on 20:39
Nokia may be introduce their first android phone. But the nokia doesn't use the google devoloped Android. The Amazon use the OS on thier Kindle fire tablet, like that Nokia use an operating system maintained by their own may be use. This operating system named Nomandy (officially not published) . And this mobile might be in the asha series range. And the cost of product also around the Asha series mobile. But in compared to Asha platform this OS can run more apps rather than asha.
Micromax canvas Turbo specifications and unboxing
Posted By:
I am Nothing
on 20:13
Turbo Looking Image!!!
Specifications
| General | |
| Alternate names | A250 |
| Release date | October 2013 |
| Form factor | Touchscreen |
| Dimensions (mm) | 128.30 x 71.00 x 8.60 |
| Battery capacity (mAh) | 2000 |
| Removable battery | No |
| Colours | Midnight Blue, Pristine White |
| SAR value | NA |
| Display | |
| Screen size (inches) | 5.00 |
| Touchscreen | Yes |
| Touchscreen type | Capacitive |
| Resolution | 1080x1920 pixels |
| Pixels per inch (PPI) | 441 |
| Colours | 16.7M |
| Hardware | |
| Processor | 1.5GHz quad-core |
| Processor make | MediaTek |
| RAM | 2GB |
| Internal storage | 16GB |
| Camera | |
| Rear camera | 13-megapixel |
| Flash | Yes |
| Front camera | 5-megapixel |
| Software | |
| Operating System | Android 4.2 jelly bean |
| Java support | Yes |
| Browser supports Flash | No |
| Connectivity | |
| Wi-Fi | Yes |
| Wi-Fi standards supported | NA |
| GPS | Yes |
| Bluetooth | Yes, v 4.00 |
| NFC | No |
| Infrared | No |
| DLNA | No |
| Wi-Fi Direct | No |
| MHL Out | No |
| HDMI | No |
| Headphones | 3.5mm |
| FM | Yes |
| USB | Micro-USB |
| Charging via Micro-USB | Yes |
| Proprietary charging connector | No |
| Proprietary data connector | No |
| Number of SIMs | 2 |
| SIM 1 | |
| SIM Type | Micro-SIM |
| GSM/ CDMA | GSM |
| 2G frequencies supported | GSM 850/ 900/ 1800/ 1900 |
| 3G | Yes |
| 3G frequencies supported | 2100 |
| SIM 2 | |
| SIM Type | Regular |
| GSM/ CDMA | GSM |
| 2G frequencies supported | GSM 850/ 900/ 1800/ 1900 |
| 3G | No |
| 3G frequencies supported | NA |
| Sensors | |
| Compass/ Magnetometer | Yes |
| Proximity sensor | Yes |
| Accelerometer | Yes |
| Ambient light sensor | Yes |
| Gyroscope | Yes |
| Barometer | No |
| Temperature sensor | No |
Unboxing Complete video
Monday 23 December 2013
Internet Download Manager latest version free download
Posted By:
I am Nothing
on 21:18
Internet Download Manager
(IDM) is a tool to increase download speeds by up to 5 times, resume
and schedule downloads. Comprehensive error recovery and resume
capability will restart broken or interrupted downloads due to lost
connections, network problems, computer shutdowns, or unexpected power
outages. Simple graphic user interface makes IDM user friendly and easy
to use.Internet Download Manager has a smart download logic accelerator
that features intelligent dynamic file segmentation and safe multipart
downloading technology to accelerate your downloads. Unlike other
download managers and accelerators Internet Download Manager segments
downloaded files dynamically during download process and reuses
available connections without additional connect and login stages to
achieve best acceleration performance.
Note: This is only for 30 Days Trial- After that you should purchase the licence key from the IDM website
Wifi hacking software using wifi hacker for PC
Posted By:
I am Nothing
on 21:08
How to Hack a Wifi network
An internet connection has become a basic necessity in our modern lives. Wireless hot-spots (commonly known as Wi-Fi) can be found everywhere! If you have a PC with a wireless network card, then you must have seen many networks around you. Sadly most of these networks are secured with a network security key. Have you ever wanted to use one of these networks? You must have desperately wanted to check your mail when you shifted to your new house. The hardest time in your life is when your internet connection is down. Hacking those Wi-Fi passwords is your answer to temporary internet access.
An internet connection has become a basic necessity in our modern lives. Wireless hot-spots (commonly known as Wi-Fi) can be found everywhere! If you have a PC with a wireless network card, then you must have seen many networks around you. Sadly most of these networks are secured with a network security key. Have you ever wanted to use one of these networks? You must have desperately wanted to check your mail when you shifted to your new house. The hardest time in your life is when your internet connection is down. Hacking those Wi-Fi passwords is your answer to temporary internet access.
How to create a bootable USB for ubuntu OS
Posted By:
I am Nothing
on 20:12
Should Know about Ubuntu
Linux was already established as an enterprise server platform in 2004, but free software was not a part of everyday life for most computer users. That's why Mark Shuttleworth gathered a small team of developers from one of the most established Linux projects – Debian – and set out to create an easy-to-use Linux desktop: Ubuntu.The vision for Ubuntu is part social and part economic: free software, available to everybody on the same terms, and funded through a portfolio of services provided by Canonical.
To run Ubuntu from a USB stick, the first thing you need to do is insert a USB stick with at least 2GB of free space into your PC.
To Know more about ubuntu click here
Now lets come on How to bootable a ubuntu using USB
Note:-To run Ubuntu from a USB stick, the first thing you need to do is insert a USB stick with at least 2GB of free space into your PC.
STEP1: First of all you need to install the software to create a bootable USB thats called Universal USB Installer
STEP 2: Open the software and select the below category from the list
STEP 3: Click on Browse button and open your downloaded ubuntu ISO file
STEP 4: After opening the file click on Create button to make a bootable USB,
This may take a few minutes . Wait for that
Note: Please don't remove pendrive while its running for creating the bootable file
Microsoft security essentials latest version free download
Posted By:
I am Nothing
on 19:49
About Microsoft security essentials
Use Microsoft Security Essentials to help guard against
viruses, spyware, and other malicious software. It provides real-time
protection for your home or small business PCs.
Microsoft Security Essentials
is free* and we designed it to be simple to install and easy
to use. It runs quietly and efficiently in the background so you don't
have to worry about interruptions or making updates.
( from the Official Microsoft website )
You may also Like this
Norton Internet Security 2014 - Security Software | India free download
Thursday 12 December 2013
Download Tubemate 2.0.9 free for Android
Posted By:
I am Nothing
on 21:33
Hello , Would you like to download the videos from youtube with various resolution then you should use this amazing android application to your need::The tubemate application have alot of features including the resuming capability...and you can set the download speed for your tubemate videos and much more functions.
Then why you are waiting download the latest tubemate application for your android device
Saturday 7 December 2013
convert currencies using Currency convertor app for android mobile
Posted By:
I am Nothing
on 20:08
 Do you need any help for converting the currencies of different countries, then download this useful android application for you mobile with free from Google Play:
Do you need any help for converting the currencies of different countries, then download this useful android application for you mobile with free from Google Play:About:Simple Currency Converter - Track Currencies from around the world. Easily convert between your favorite currencies. Graph currency pairs over time, get the latest news on each currency. Set up portfolios of currencies for easy tracking.
The newest version following features
New in 2.4
- Upgradeable to ADS FREE
- Bug fix on first startup
- Move2SD
- Multiple bug fixes
- Lighter download requirements
- Bug fix on first startup
- Move2SD
- Multiple bug fixes
- Lighter download requirements
Friday 6 December 2013
tata docomo offers new prepaid plans
Posted By:
I am Nothing
on 21:44
Tata Docomo offered a good prepaid plan for the customers those who are looking for 3G with the voice calls
you just recharge with Rs 251 and you will get 1 GB 3g data and 200rs will be credited to your account.
bsnl 3g internet hacking 2014 100% working
Posted By:
I am Nothing
on 21:33
Hello, Today i will discuss about the BSNL 3g hacking , this is 100 % working trick and there have no hidden trick. Its just a BSNL internet settings and that settings can make more data usage. It means that you can save 1000% data by using this APN
suppose if you are recharged with the BSNL 3g Rs 139 for 1 GB, you can use around 8-10 GB by using this BSNL settings,
Just follow the below settings to make this helpful trick
suppose if you are recharged with the BSNL 3g Rs 139 for 1 GB, you can use around 8-10 GB by using this BSNL settings,
Just follow the below settings to make this helpful trick
1: create a new settings
2.Name: BSNLINTERNET
APN: BSNLSTREAM
airtel 3G internet speed improved by 25% faster advanced for 2014
Posted By:
I am Nothing
on 20:07
hello welcome, are you an airtel mobile subscriber, then you should know this, airtel offers more speed than other network providers, advanced for 2014 airtel gives you 25 % more speed in your 3g plans :
Your battery lasts 20% longer
airtel 3G network boasts of smart features that help you
save your smartphone's battery life. Yes, that's true. Our advanced
network controls devices and puts them in energy conservation state. The
updates of the apps are done periodically at low energy states that
help in saving battery life and thus, improving your handset's
performance!
idea gprs 3g hack 2014 best settings
Posted By:
I am Nothing
on 19:54
you may already tried many proxy settings for gprs hacking. but its many of the time may not be working properly. the new idea gprs settings will give you more data for your 3g plan or for 2g.
this is nothing too.
its just simple and may not be working 100%
 Follow the below step :
Follow the below step :
1: create a setting
2:name: ideainternet
apn:internet
proxy:23.0.1271.64
port 8080
authentication mode:normal
3.save your settings and restart your phone
just try this may be working .................
thanks for visiting , comment please
this is nothing too.
its just simple and may not be working 100%
 Follow the below step :
Follow the below step : 1: create a setting
2:name: ideainternet
apn:internet
proxy:23.0.1271.64
port 8080
authentication mode:normal
3.save your settings and restart your phone
just try this may be working .................
thanks for visiting , comment please
Sunday 24 November 2013
Folder lock without any software for all windows versions
Posted By:
I am Nothing
on 11:29
hello guyz you can protect your folder from unauthorized users. Its very simple and you can use a password to protect the file.
I will explain how its
Follow the below steps to lock a folder
STEP 1: copy the below text code into notepad
I will explain how its
Follow the below steps to lock a folder
STEP 1: copy the below text code into notepad
cls
@ECHO OFF
title Folder Private
if EXIST "HTG Locker" goto UNLOCK
if NOT EXIST Private goto MDLOCKER
:CONFIRM
echo Are you sure you want to lock the folder(Y/N)
@ECHO OFF
title Folder Private
if EXIST "HTG Locker" goto UNLOCK
if NOT EXIST Private goto MDLOCKER
:CONFIRM
echo Are you sure you want to lock the folder(Y/N)
Norton Internet Security 2014 - Security Software | India free download
Posted By:
I am Nothing
on 11:12
- Keeps you safe when you surf, shop and bank online
- Warns you about social media scams and suspicious content
- Stops both today's and tomorrow's threats
- Blocks infected and dangerous downloads
- Reduces PC startup time and boosts performance
CLICK HERE to download
Subscribe to:
Posts (Atom)